Ntrights Utility Download
- Ntrights Command
- Ntrights Utility Download Free
- Ntrights Utility Download Windows 10
- Ntrights Utility Downloads
- Ntrights.exe
- Ntrights Utility Download Software
When setting up new virtual machines for Team Foundation Server 2010, I find myself having to manually create the four amigos: TFSSERVICE, TFSREPORTS, TFSBUILD, and WSSSERVICE (per the installation guide). Needless to say, this gets quite old, so I set out to automate this process.
- 3.1.3.3 Granting rights with the NTRights.exe Utility. 3–3 3.2 CREATING NT JOBS 3–3 3.2.1 Windows NT Execution Methods 3–3 3.2.2 Windows NT Example Job 3–3 CHAPTER 4 GETTING STARTED ON UNIX 4–1 4.1 GETTING READY FOR UNIX 4–1 4.1.1 Define Unix Usernames in JAMS 4–1 4.1.2 Verify that the rexec daemon is enabled on your target 4–1.
- You can use the NTRights.exe utility to grant or deny user rights to users and groups from a command line or a batch file. The NTRights.exe utility is included in the Windows NT Server 4.0 Resource Kit Supplement 3.
First, I checked out Grant Holliday’s post from 2007 on Hands Free TFS Installation. I was only interested in the part where he creates the accounts and sets the permissions. His approach uses a (.bat) batch file, so he’s limited to using “NET USER” commands such as “net user TFSSERVICE * /DOMAIN /ADD /EXPIRES:NEVER”. I wanted to specify account description and have more control, so I decided to integrate his ideas with mine into a (.vbs) VBScript file. I also added code to create groups, such as the TFS Administrators group, which I always suggest having.
1. Download my script
It’s at the bottom of this post.
3.1.3.3 Granting rights with the NTRights.exe Utility The NTRights.exe utility is included in the Windows NT Server 4.0 Resource Kit supplement 3 and in the Windows 2000 Resource Kit. If you have this utility you can grant the 'Log on as a batch job' right with a command like this.
2. Obtain Microsoft’s ntrights.exe utility
It’s part of the free download of the Windows Server 2003 Resource Kit Tools. Download the tools and then install. Since you only need the ntrights.exe tool, it seems silly to install everything else, especially when I try to keep my VMs as small as possible. I used a snapshot VM so I could revert back, then installed the tools, copied out the one file, and reverted. If you trust me, then you can just download the ntrights.zip at the bottom (just don’t tell Microsoft).
Ntrights Command
3. Customize the script
You may want to change the computer name, password, and account names. These are easy search/replace operations.
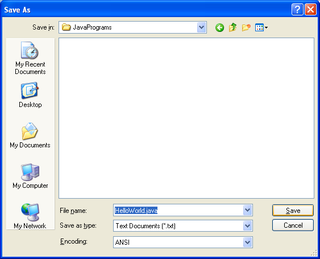
4. Keep the files together
I opted to put the tfsaccounts.vbs and ntrights.exe in the root of C:Program Files for simplicity and to not clutter up my C: root folder.
Attachments: tfsaccounts.zip, ntrights.zip
-->By Mark Russinovich
Published: October 15, 2020
Download AccessChk(957 KB)
Run now from Sysinternals Live.
Ntrights Utility Download Free
Introduction
As a part of ensuring that they've created a secure environment Windowsadministrators often need to know what kind of accesses specific usersor groups have to resources including files, directories, Registry keys,global objects and Windows services. AccessChk quickly answers thesequestions with an intuitive interface and output.
Installation
AccessChk is a console program. Copy AccessChk onto your executablepath. Typing 'accesschk' displays its usage syntax.

Using AccessChk
Usage: accesschk [-s][-e][-u][-r][-w][-n][-v]-[f<account>,...][[-a]|[-k]|[-p [-f] [-t]]|[-h][-o[-t <object type>]][-c]|[-d]] [[-l[-i]]|[username]] <file, directory, registry key, process,service, object>
| Parameter | Description |
|---|---|
| -a | Name is a Windows account right. Specify '*' as the name to show all rights assigned to a user. Note that when you specify a specific right, only groups and accounts directly assigned to the right are displayed. |
| -c | Name is a Windows Service, e.g. ssdpsrv. Specify '*' as the name to show all services and 'scmanager' to check the security of the Service Control Manager. |
| -d | Only process directories or top-level keys |
| -e | Only show explicitly set-Integrity Levels (Windows Vista and higher only) |
| -f | If following -p, shows full process token information including groups and privileges. Otherwise is a list of comma-separated accounts to filter from the output. |
| -h | Name is a file or printer share. Specify '*' as the name to show all shares. |
| -i | Ignore objects with only inherited ACEs when dumping full access control lists. |
| -k | Name is a Registry key, e.g. hklmsoftware |
| -l | Show full security descriptor. Add -i to ignore inherited ACEs. |
| -n | Show only objects that have no access |
| -o | Name is an object in the Object Manager namespace (default is root). To view the contents of a directory, specify the name with a trailing backslash or add -s. Add -t and an object type (e.g. section) to see only objects of a specific type. |
| -p | Name is a process name or PID, e.g. cmd.exe (specify '*' as the name to show all processes). Add -f to show full process token information, including groups and privileges. Add -t to show threads. |
| -q | Omit Banner |
| -r | Show only objects that have read access |
| -s | Recurse |
| -t | Object type filter, e.g. 'section' |
| -u | Suppress errors |
| -v | Verbose (includes Windows Vista Integrity Level) |
| -w | Show only objects that have write access |
If you specify a user or group name and path, AccessChk will report theeffective permissions for that account; otherwise it will show theeffective access for accounts referenced in the security descriptor.
By default, the path name is interpreted as a file system path (use the'pipe' prefix to specify a named pipe path). For each object,AccessChk prints R if the account has read access, W for write access,and nothing if it has neither. The -v switch has AccessChk dump thespecific accesses granted to an account.
Examples
The following command reports the accesses that the Power Users accounthas to files and directories in WindowsSystem32:
accesschk 'power users' c:windowssystem32
This command shows which Windows services members of the Users grouphave write access to:
accesschk users -cw *

To see what Registry keys under HKLMCurrentUser a specific account hasno access to:
Ntrights Utility Download Windows 10
accesschk -kns austinmruss hklmsoftware
To see the security on the HKLMSoftware key:
accesschk -k hklmsoftware
To see all files under UsersMark on Vista that have an explicitintegrity level:
Ntrights Utility Downloads
accesschk -e -s c:usersmark
Ntrights.exe
To see all global objects that Everyone can modify:
Ntrights Utility Download Software
accesschk -wuo everyone basednamedobjects
Download AccessChk(957 KB)
Run now from Sysinternals Live.